Summary: A supply chain vulnerability assessment helps organizations identify and prioritize the weak points most likely to disrupt operations, from single-source dependencies and cyber risk to regulatory and geopolitical exposure. For supply chain managers, vulnerability assessment is increasingly part of formal due diligence because regulations such as CSDDD and LkSG require companies to find and address risk across supplier tiers. The result is a more resilient supply chain and earlier action on threats before cost, backlog, or compliance failures escalate.

A supply chain vulnerability assessment is a structured process for identifying, evaluating, and prioritizing risks that could disrupt an organization’s supply chain. These risks range from single-source supplier dependencies and geopolitical instability to regulatory compliance failures and cyberattacks. In 2025–2026, the business case for conducting regular vulnerability assessments has intensified dramatically. Specifically, the EU Corporate Sustainability Due Diligence Directive (CSDDD) and Germany’s LkSG explicitly require companies to identify and address human rights and environmental risks across supply chain tiers. As a result, formal vulnerability assessment is now a legal obligation — not just a best practice.
According to the Institute for Supply Management, the Backlog of Orders Index for the manufacturing sector reached an unprecedented 71%. Global disruptions cascaded through supply networks, creating this surge. Consequently, organizations without proactive vulnerability assessments faced the steepest operational consequences.
The financial cost of supply chain failures remains severe. Backorder fulfillment expenses have soared from $15 to $20 USD per incident. Furthermore, these direct costs do not capture reputational damage, customer churn, or regulatory penalties. A supply chain vulnerability assessment provides the systematic framework needed to safeguard operations before disruptions occur.
Understanding Supply Chain Vulnerability
Businesses experience vulnerability in their supply chain when unidentified risks from both internal and external sources expose them to disruption. In fact, the more a company’s critical operations depend on a narrow set of suppliers, geographies, or logistics routes, the more vulnerable it becomes. Ultimately, supply chain vulnerability shows up most visibly in a company’s ability — or inability — to meet end customer demands reliably and in compliance with applicable regulations.
Under CSDDD and LkSG, supply chain vulnerability now carries a direct legal dimension. In other words, organizations that fail to identify and address human rights or environmental risks in their supply chains face mandatory corrective action obligations and potential civil liability.
Examples of Supply Chain Vulnerabilities
To effectively understand and address supply chain risk, organizations must recognize vulnerabilities across two primary categories. The first is internal weaknesses within their own operations and processes. On the other hand, the second is external threats originating from outside the supply chain.
Internal Vulnerabilities
Internal vulnerabilities are weaknesses or risks stemming from within the supply chain. They include issues with design, structure, processes, practices, and the culture of participating organizations. Common internal vulnerabilities include:
- Insufficient visibility and transparency: Failing to monitor and trace the movement of materials, information, and finances throughout the supply chain can result in inefficiencies, errors, fraudulent activities, or theft — and makes it impossible to produce the documented audit trail required by CSRD and LkSG.
- Subpar supplier performance and dependability: Failing to meet customer or regulatory standards can lead to defects, recalls, complaints, or penalties. Under CSDDD, persistent supplier non-compliance with human rights or environmental standards triggers mandatory escalation and corrective action obligations.
- Lack of flexibility and adaptability: Struggling to adjust to shifts in demand, supply, or the regulatory environment can result in delays, shortages, overstock, or product obsolescence — and can leave organizations exposed during sudden regulatory changes such as new forced labor import restrictions.
- Misalignment of incentives and goals: Divergent interests and objectives among supply chain partners can create conflicts, mistrust, or opportunism — particularly when sustainability and compliance targets are not formally embedded in supplier contracts and audit protocols.
External Vulnerabilities
External vulnerabilities are threats or hazards originating outside the supply chain. They come from the market, regulatory environment, geopolitical landscape, or natural world. Key external vulnerabilities include:
- Market unpredictability and volatility: Fluctuations in demand and supply conditions significantly impact pricing, availability, and profitability across the supply chain — as demonstrated by the commodity price spikes and freight rate surges of recent years.
- Competitive disruption: The rise of new competitors, technologies, or business models can disrupt the market position and value proposition of existing supply chain arrangements, requiring rapid supplier diversification.
- Regulatory and legal changes: The implementation of new laws such as CSDDD, LkSG, the EU CSRD, and the US Uyghur Forced Labor Prevention Act (UFLPA) introduces new due diligence requirements, compliance costs, and potential import restrictions that can fundamentally reshape supply chain structures.
- Social and environmental concerns: ESG-related issues — including forced labor allegations, environmental violations, and human rights controversies — can damage supplier relationships, trigger regulatory investigations, and expose buying companies to reputational and legal liability under modern supply chain due diligence laws.
- Natural disasters and health crises: The occurrence of natural disasters or pandemics can disrupt infrastructure, transportation, and communication networks across supply chains — as demonstrated by recent disruptions that exposed dangerous concentration risk in single-region sourcing strategies.
What are the Driving Factors?
Structure of Supply Chain
Coordination becomes significantly more challenging and error-prone in supply chains with greater numbers of tiers, geographic spread, and supplier dependencies. In particular, multi-tier supply chains create visibility gaps that regulators increasingly target. For example, CSDDD requires companies to map risks not just at the first tier but across the entire supply chain, including raw material extraction.
Regular audits of your supply chain serve as an effective strategy to mitigate vulnerabilities and drive structural improvements. This practice leads to more resilient supply chain design. Moreover, it acts as a proactive measure to reduce regulatory exposure. This is particularly relevant because LkSG-covered companies must conduct risk analyses at least annually and whenever significant changes occur in their operations or supply base.
Initiating supply chain audits and internal inspections can demand significant time and cost. However, digital solutions like the ESG Checklist make the process accessible at scale. These digital checklists enable teams to gather supplier information via mobile devices, generate real-time compliance reports, and create the documented audit trail that modern supply chain regulations require.
Complexity in Organization
As companies develop more complex products, enter new markets, and engage deeper supplier tiers, supply chain risk management complexity escalates accordingly. Therefore, the decision-making processes within management must continuously evolve the organization’s supply chain risk framework. This evolution must keep pace with internal growth and external regulatory demands — including the expanding scope of CSRD double-materiality assessments.
Data Management
Complex supply chains involve multiple stages of data exchange between suppliers and final consumers. As a result, communication accuracy can degrade as information passes through many layers of a supply chain network. In the context of CSDDD and CSRD compliance, data integrity is especially critical. Specifically, organizations must demonstrate that the supplier data underpinning their due diligence decisions is current, accurate, and traceable to verified sources.
What’s the Purpose of a Supply Chain Vulnerability Assessment?
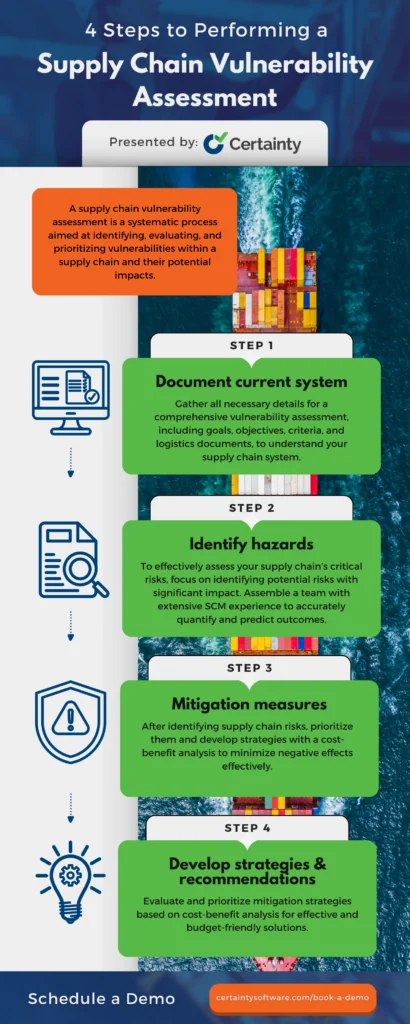
A supply chain vulnerability assessment systematically identifies, evaluates, and prioritizes vulnerabilities along with their potential operational, financial, and regulatory impacts. The purpose is to make the supply chain more resilient and operationally reliable. Additionally, this process creates the documented risk identification framework that CSDDD, LkSG, and CSRD compliance require. Specifically, there are four essential phases involved in conducting a thorough supply chain vulnerability assessment.

30+ Audit and inspection checklists free for download.
4 Steps to Perform a Supply Chain Vulnerability Assessment
Step 1: Document Current System
Begin by gathering data and documenting your existing supply chain framework and all outsourcing arrangements. Compile all relevant details needed for a thorough vulnerability evaluation. For example, these include strategic objectives, supplier contracts, logistics management documentation, ESG commitments, and any existing risk assessments. Notably, under CSDDD and LkSG, companies must document the scope of their supply chain and the criteria they use to prioritize risk analysis efforts.
This comprehensive baseline will provide your team with the necessary insights for informed risk prioritization decisions. Furthermore, it forms the documented foundation of your supply chain due diligence program.
Step 2: Identify Hazards
Focus your assessment team on identifying potential risks with significant financial, operational, or regulatory impact. This includes supplier concentration risk, single-source dependencies, forced labor exposure in high-risk geographies, environmental violations, and cybersecurity weaknesses. Similarly, once you identify each risk, quantify its potential impact and likelihood.
Assembling a cross-functional supply chain vulnerability assessment team is critical for capturing the full range of modern supply chain risks. This team should include procurement, legal, compliance, and sustainability professionals. In particular, they must address human rights and environmental risks now covered under CSDDD and LkSG.
Step 3: Mitigation Measures
Once you have identified and prioritized risks, develop strategies to minimize or eliminate their negative effects. Additionally, incorporate a cost-benefit analysis during this phase to ensure mitigation measures are both practically effective and financially viable. Under CSDDD, mitigation plans for identified human rights and environmental risks must include documented timelines, responsible parties, and measurable outcomes.
Step 4: Develop Strategies/Recommendations
Evaluate and prioritize the mitigation strategies that deliver the best outcomes within your operational and financial constraints. A thorough cost-benefit analysis will help determine which measures are most effective and financially sustainable. To that end, formalize these strategies into a documented risk management plan. Under LkSG and CSDDD, organizations must review and update this plan at least annually. They must also update it whenever material changes in the supply chain risk landscape occur.
About Certainty Software
Certainty Software is a purpose-built inspection, audit, and compliance management solution designed to strengthen supply chain resilience. It simplifies the collection, reporting, and management of supply chain data and compliance issues. As a result, Certainty empowers organizations to drive performance, meet regulatory due diligence obligations under CSDDD, LkSG, and CSRD, and respond to emerging risks with speed and confidence.
With Certainty Software, teams can design and tailor audit forms for the full range of supply chain inspections. These span from environmental compliance checks to human rights due diligence assessments. Moreover, organizations can track and evaluate the quality and compliance performance of products and processes throughout the supply chain. They can also adapt swiftly to shifts in demand, supply conditions, or regulatory requirements with real-time, data-driven decisions. This enables effective alignment of sustainability and compliance goals across the entire supplier network.
Certainty Software also delivers dynamic real-time reports and interactive dashboards. These provide a comprehensive view of supply chain performance, compliance status, and emerging risk indicators. In addition, the platform generates and assigns corrective and preventive actions automatically. It monitors their progress through to verified completion. Ultimately, this creates the documented audit trail that modern supply chain due diligence regulations require.
Interested in learning more? Schedule a quick demo to discover how Certainty Software can strengthen your supply chain vulnerability management and regulatory compliance program.
Frequently Asked Questions (FAQs)
What is the difference between a supply chain risk assessment and a vulnerability assessment?
A supply chain risk assessment broadly identifies threats that could disrupt operations. A supply chain vulnerability assessment goes further by examining the specific internal and external weaknesses that make a supply chain susceptible to those threats. Vulnerability assessments are more granular, examining the structural and process-level factors — such as single-source dependencies, poor data visibility, or misaligned supplier incentives — that amplify the impact of disruptions when they occur. Both are required components of a CSDDD-compliant due diligence program.
How does CSDDD affect supply chain vulnerability assessments?
The EU Corporate Sustainability Due Diligence Directive (CSDDD) requires large companies to systematically identify actual and potential adverse impacts on human rights and the environment across their supply chains — precisely what a supply chain vulnerability assessment is designed to do. CSDDD mandates that companies embed risk-based due diligence processes into their operations, establish supplier engagement and remediation processes, and report publicly on their due diligence activities. Organizations that already conduct formal supply chain vulnerability assessments will have a significant compliance advantage as CSDDD obligations phase in through 2027–2029.
How frequently should a supply chain vulnerability assessment be updated?
Best practice — and LkSG’s explicit requirement — is to review and update the supply chain vulnerability assessment at least annually, and additionally whenever significant changes occur, such as onboarding new high-risk suppliers, entering new sourcing geographies, or following a significant disruption event. CSDDD similarly requires companies to maintain ongoing due diligence processes rather than treating risk assessments as one-time exercises.
You may also be interested in:



