
The complexity of managing global supply chains has significantly escalated over the past ten years, a situation further exacerbated by the Pandemic. According to the Institute for Supply Management, the Backlog of Orders Index for the manufacturing sector reached an unprecedented 71% in May 2021.
This surge is primarily attributed to extended lead times and product scarcities. Moreover, the expenses incurred to address these backorders have soared from 15 to USD 20 per backorder fulfillment. However, there are resources like the Supply Chain Vulnerability Assessment that can aid in safeguarding your supply chain from such predicaments.
Understanding Supply Chain Vulnerability
Businesses experience vulnerability in their supply chain when exposed to the blind risks of both internal and external supply chain disruptions. The more responsive the critical components of a business’s supply chain are to risks, the more vulnerable the business is. Ultimately, your business’s ability to meet your end customer’s demands suffers the most when supply chain vulnerability is prevalent.
Examples of Supply Chain Vulnerabilities
To effectively grasp the risks present in the supply chain, it’s essential to understand the dual categories of vulnerabilities: those that arise internally within the organization, and those that stem from external factors.
Internal Vulnerabilities
Internal vulnerabilities refer to weaknesses or risks that stem from within the supply chain, including aspects like the design, structure, processes, practices, and culture of those involved in the supply chain. Some instances of internal vulnerabilities include:
- Insufficient visibility and transparency: Failing to monitor and trace the movement of materials, information, and finances throughout the supply chain can result in inefficiencies, mistakes, fraudulent activities, or theft.
- Subpar performance and dependability: Failing to meet customer or regulatory standards and expectations can lead to issues such as defects, recalls, complaints, or penalties.
- Lack of flexibility and adaptability: Struggling to adjust to shifts in demand, supply, or the environment can result in delays, shortages, overstock, or product obsolescence.
- Misalignment of incentives and goals: The divergence of interests and objectives among the supply chain partners can create conflicts, mistrust, or opportunism.
External Vulnerabilities
External vulnerabilities refer to external threats or hazards that stem from sources outside the supply chain, including the market, industry, society, or nature. Some instances of external vulnerabilities include:
- Market unpredictability and volatility: Fluctuations in demand and supply conditions can have a significant impact on the pricing, availability, and profitability within the supply chain.
- Competition and challenges: The rise of new competitors, technologies, or business strategies can bring about disruptions to the current market position and value proposition of the supply chain.
- Changes in regulations and laws: The implementation or alterations of laws, policies, or standards may introduce new requirements, limitations, or expenses to the supply chain.
- Social and environmental concerns: Issues related to social or environmental matters can influence the reputation, credibility, and sustainability of the supply chain.
- Natural disasters and health crises: The occurrence or spread of natural disasters or pandemics can create disruptions to the infrastructure, transportation, and communication networks in the supply chain.
What are the Driving Factors?
Structure of Supply Chain
Coordination can become more challenging and prone to errors in supply chains that have a greater number of options, businesses, and dependencies on suppliers.
Regular audits of your supply chain serve as an effective strategy to mitigate supply chain vulnerabilities. This practice can lead to unexpected enhancements in your supply chain structure and acts as a proactive measure to decrease your supply chain vulnerability.
Initiating supply chain audits and internal inspections can be a hurdle for many businesses due to the demands of time and cost. However, online solutions like the ESG Checklist for supplier checklists are accessible. These digital checklists aid in gathering supplier information through mobile devices and generating real-time reports, enabling swift and efficient decision-making.
Complexity in Organization
As companies develop more intricate products and procedures, the significance of supply chain risk management escalates. The decision-making of your management must consistently modify the organization’s supply chain framework as internal progression becomes more intricate.
Data Management
Intricate supply chains encompass numerous stages of data exchange between suppliers and final consumers. Communication from the origin to the intended destination of a supply chain can become distorted as information is passed through the multiple layers of a supply chain network.
What’s the Purpose of a Supply Chain Vulnerability Assessment?
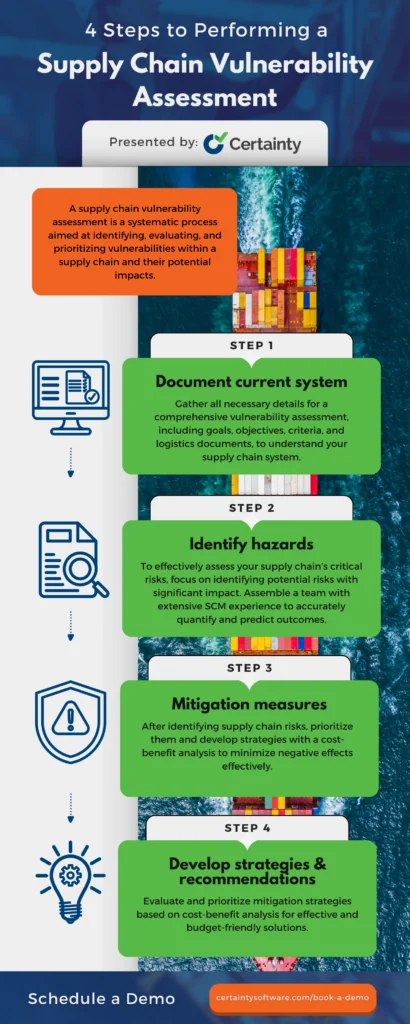
Finding, assessing, and prioritizing supply chain vulnerabilities and their possible effects requires a rigorous approach, which is what’s involved in conducting an assessment of supply chain vulnerabilities. This assessment makes the supply chain more resilient and performs better, which makes it easier to create and implement mitigation plans that work. There are four essential phases involved in doing a supply chain vulnerability assessment.

30+ Audit and inspection checklists free for download.
4 Steps to Perform a Supply Chain Vulnerability Assessment
Step 1: Document Current System
Besides gathering data and outlining your existing supply chain framework and outsourcing procedures, it’s vital to accumulate all pertinent details for a thorough vulnerability evaluation. Consider including your goals, objectives, criteria, logistics management documents, and any other pertinent details to paint a clear picture of your supply chain system.
This holistic approach will provide your team with the necessary insights to make informed decisions and strengthen your overall supply chain strategy.
Step 2: Identify Hazards
To effectively assess your supply chain’s most critical risks, your assessment team should focus on identifying potential risks that could have a significant financial impact. Once these risks are pinpointed, it is essential to quantify their impact accurately.
This can be a challenging task, which is why it is crucial to assemble a Supply Chain Vulnerability Assessment team consisting of individuals with extensive knowledge and experience in supply chain management. With their knowledge at your disposal, you’ll be able to predict with confidence the possible outcomes and duration of these hazards.
Step 3: Mitigation Measures
Once you have pinpointed the potential risks to your supply chain and prioritized them accordingly, the next step is to devise effective strategies to minimize or eliminate their negative effects. It is crucial to incorporate a thorough cost-benefit analysis during this phase of your vulnerability assessment to ensure that the chosen solutions are both practical and financially advantageous.
Step 4: Develop Strategies/Recommendations
Once you have gathered all the necessary data and brainstormed potential solutions, the next crucial step is to carefully evaluate and prioritize the mitigation strategies that will yield the best results while staying within your budget. Conducting a thorough cost-benefit analysis will help you determine which measures are not only effective but also financially feasible in the long run.
About Certainty Software
Certainty Software is a cutting-edge inspection software solution designed to enhance your supply chain’s strength and efficiency. By simplifying the collection, reporting, and management of supply chain data and issues, it empowers you to drive performance and resilience to new heights.
With Certainty Software, you have the power to design and tailor forms for a wide range of supply chain inspections and audits. You can also track and assess the quality and dependability of products and processes throughout the supply chain, enabling you to adapt swiftly to shifts in demand, supply, or environmental factors with well-informed and timely decisions. This allows you to harmonize the goals and interests of your supply chain partners effectively.
Certainty Software also offers dynamic real-time reports and interactive dashboards that offer a detailed and holistic insight into supply chain performance and potential risks. Additionally, it empowers you to effortlessly generate and assign corrective and preventive actions, while monitoring their advancement and finalization.
Interested in learning more about Certainty Software? Schedule a quick demo to discover how Certainty Software can bolster your supply chain management.
You may also be interested in:



